

Phoenix BIOS Editor decompresses a single ROM image automatically. It proceeds to the small ROM modules that are part of the BIOS. After completing the modification of the ROM image, the utility adds custom modifications to the new BIOS image. The latter can be written to flash memory. The utility allows users to make changes to a previously created ROM image without using the source code.
The Windows Phoenix BIOS Editor application has a simple interface to modify the Phoenix BIOS Rel. 6 and then there is no need to reinstall the BIOS afterwards. It supports unpacking, replacing and repackaging components in the BIOS image and also allows you to change settings and modify the application for the actual BIOS itself.
Rebuild BIOS
For primary BIOS files, such as the one included in VMware, a number of command line utilities included in Phoenix Bios Editor (or available from Intel) can be used for rebuilding. Later, when testing on a real PC, it was necessary to save the BIOS in more than just the primary format, so the GUI version of Phoenix Bios Editor was used as the re-build tool. Unfortunately, this means that it is not possible to simply have a single application that can be run on a system so that it infects the BIOS, at least not without using pre-built tools.
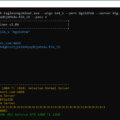
This means that infecting the BIOS is a three-step process that requires some manual intervention, mainly for re-building. The Phoenix BIOS Editor with an open BIOS image is shown below:
The Phoenix BIOS Editor was not designed for module swapping, but still provides this feature. When the BIOS image is opened for the first time, all BIOS modules will be extracted to disk in a folder located in:
C:\Program Files\Phoenix BIOS Editor\TEMP\The unpack module can be copied from this folder, patched and replaced. Phoenix BIOS Editor will not allow you to save the BIOS unchanged, so to save the BIOS we should change some string value and then change it back (or just leave it that way).
The BIOS rootkit source code and patching scripts can be downloaded from the links at the end of this article if you want to do it all yourself.
Download Phoenix BIOS Editor
If you like to read such articles and want to support the author, then you can subscribe to our telegram channel and recommend us to your friends, this will help a lot to support our project! Telegram:
Be the first to know all the news, read more about cryptocurrencies and mining at CRYPTO-MINING.BLOG.










No Comments